What Caused Mark Zuckerberg's Social Media Accounts Hack & What That Teaches Us About Password Security
Amsterdam, NL - February 23, 2017 -
Those of us who have a Facebook account must have come across a security tip that says: “Don’t use your Facebook password anywhere else online”. Unfortunately, it seems that Facebook’s founder, Mark Zuckerberg, did not take his own advice seriously. According to a recent report in The Wall Street Journal, Mr. Zuckerberg’s Twitter and Pinterest accounts were taken over because he re-used a password: “dadada”.Here’s a bit of intelligence that all computer users should know: Stolen passwords are sold and bought routinely all over the Internet. In fact, since May of 2016, the website Leakedsource.com, which sells access to the stolen information, has added close to one billion records of email addresses and passwords.
Hackers use these passwords to break into other accounts (other than the accounts which these passwords originally “served”), hoping that they will stumble on users, who, like Mr. Zuckerberg, reuse their passwords in multiple accounts.
What can we do to minimize exposure to such unpleasantness? Well, to begin with, take Facebook’s advice and don’t re-use your passwords. Still, if you suspect that your account has been hacked you can use the site HaveIBeenPwned.com. to figure out if your email account has been compromised. You go to the website, enter your email address or username, and it will search through almost a billion records of accounts that have been leaked.
Another thing that you can do is to turn on the two-factor authentication for your most important accounts. For example, entering a code that’s sent to you by text message along with your usual username and password combination.
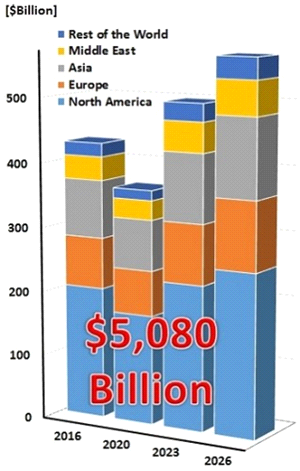
The report examines each of these markets geographically, focusing on the top 95% of global markets, in the United States, Europe, and Asia.
Furthermore, the report examines broad Cyber Weapons technology types in each of these markets and regions:
The report concentrates on the following types of Offensive Cyber Weapons:
- Distributed Denial of Service (DDoS)
- Penetration driven assault.
- Reverse rules attack
- Worms and Viruses
- Anti Distributed Denial of Service (DDoS) attack
- Anti Penetration Driven Assault
- Anti-Reverse Rules Attack
- Anti Virus